Posts By: John A
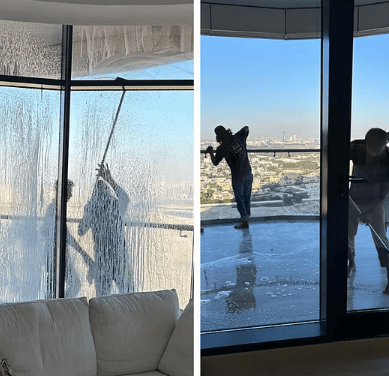
Balcony Cleaning Dubai: Elevate Your Outdoor Living Experience
Balconies in Dubai are more than just architectural features, they are personal outdoor spaces where you can relax, enjoy city views, and unwind after a…
How to Create a Winning Business Strategy Step-by-Step
A strong business strategy is what separates successful companies from those that struggle to survive. In today’s competitive global market, having a great product or…
Easy Garden Improvements That Add Value
Smart homebuyers and DIYers can add value with simple garden tweaks. Start with quick wins that boost curb appeal, then plan budget-friendly plantings that are…
What Is a Crypto Custodian?
A crypto custodian is a pivotal entity within the digital asset framework. Their primary function is to secure cryptocurrencies and digital assets, utilizing sophisticated technologies…
What Is a Crypto Custodial Wallet?
A crypto custodial wallet is a digital asset storage solution managed by third parties, emphasizing user convenience. These wallets provide enhanced security features and simplified…
Energy Storage Technology Innovations
Energy storage technology innovations are reshaping energy management and electric mobility. Recent advancements in solid-state and lithium-sulfur batteries are improving safety and energy density, while…
Edge Computing Vs Cloud Computing
The landscape of data management is increasingly shaped by edge and cloud computing. Each offers unique advantages tailored to specific operational demands. Edge computing emphasizes…
Edge Computing Security Challenges
Edge computing presents a range of security challenges linked to its decentralized nature. The proliferation of edge devices increases potential attack surfaces, complicating threat management.…
Recent Post
Cetegories
Join Our Newsletter
Straight To Your Inbox